
Cybersecurity in the Remote Work Era: Protecting Your Distributed Workforce
Introduction: The shift to remote and hybrid work models has brought unprecedented flexibility, but it's also expanded the attack surface for cyber threats. As traditional office perimeters dissolve, safeguarding your distributed workforce requires a new approach. This blog post explores the critical cybersecurity challenges of the remote era and offers actionable strategies to protect your employees and your invaluable data.

- The New Attack Surface: Home networks, personal devices, and public Wi-Fi present unique vulnerabilities. We'll discuss how phishing attacks, malware, and unsecure connections pose greater risks when employees are outside the corporate network.
- Zero Trust Architecture: Your New Mantra: Learn why a "never trust, always verify" approach is essential. We'll explain how Zero Trust ensures every user, device, and application is authenticated and authorized, regardless of location, minimizing the risk of unauthorized access.
- Endpoint Security Beyond Antivirus: Traditional antivirus isn't enough. Explore advanced endpoint detection and response (EDR) solutions that monitor activity, detect anomalies, and respond to threats in real-time across all remote devices.
- Employee Training and Awareness is Key: Your employees are your first line of defense. Discover the importance of continuous cybersecurity training, emphasizing strong password practices, identifying phishing attempts, and understanding data handling protocols in a remote setting.
- Secure Access and Data Protection: Implementing VPNs, multi-factor authentication (MFA), and secure cloud access security brokers (CASBs) are crucial. We'll detail how these technologies protect sensitive data in transit and at rest, ensuring compliance and preventing data breaches.
Conclusion: Securing a remote workforce isn't just about technology; it's about a holistic strategy that encompasses robust tools, stringent policies, and informed employees. By adopting these cybersecurity best practices, your company can confidently embrace the future of work while maintaining a strong defense against evolving threats. Let us help you build a resilient and secure remote infrastructure.
" The only limit to our realization of tomorrow is our doubts of today. "
- The New Attack Surface: Home networks, personal devices, and public Wi-Fi present unique vulnerabilities. We'll discuss how phishing attacks, malware, and unsecure connections pose greater risks when employees are outside the corporate network.
- Zero Trust Architecture: Your New Mantra: Learn why a "never trust, always verify" approach is essential. We'll explain how Zero Trust ensures every user, device, and application is authenticated and authorized, regardless of location, minimizing the risk of unauthorized access.
- Endpoint Security Beyond Antivirus: Traditional antivirus isn't enough. Explore advanced endpoint detection and response (EDR) solutions that monitor activity, detect anomalies, and respond to threats in real-time across all remote devices.
- Employee Training and Awareness is Key: Your employees are your first line of defense. Discover the importance of continuous cybersecurity training, emphasizing strong password practices, identifying phishing attempts, and understanding data handling protocols in a remote setting.
- Secure Access and Data Protection: Implementing VPNs, multi-factor authentication (MFA), and secure cloud access security brokers (CASBs) are crucial. We'll detail how these technologies protect sensitive data in transit and at rest, ensuring compliance and preventing data breaches.
Experiences More Blogs to Read

Technology
Jan 19, 2026
Digital Transformation: A Roadmap for Modern Businesses
Introduction: Digital transformation isn’t just about adopting new technology; it’s about fundamentally rethinking how your business operates, delivers value, and
By: it_admin

Technology
Jan 19, 2026
The Power of Data Analytics: Transforming Raw Data into Business Intelligence
Introduction: In today’s data-driven world, information is gold. But raw data alone isn’t enough; it’s the ability to analyze and
By: it_admin
Uncategorized
Jan 19, 2026
The Future of Cloud Computing: Trends and Predictions
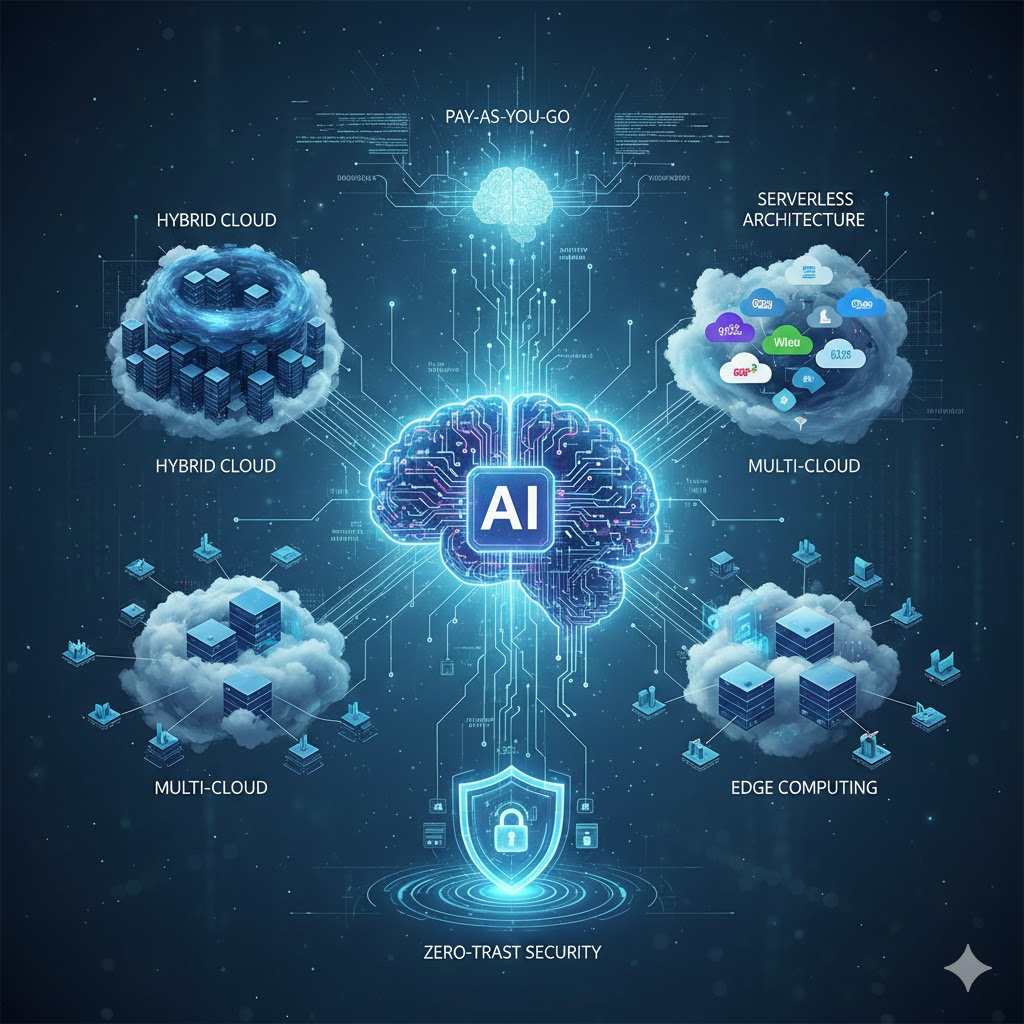
Introduction: Cloud computing has transformed the IT landscape, becoming the backbone of modern businesses. But what’s next? As technology continues
By: it_admin